Governing the Autonomous Enterprise: A Strategic Framework for OpenClaw Transformation and Agentic OS Orchestration
The global technological landscape is currently navigating a fundamental reorganization of computing paradigms, defined by a rapid transition from the conversational artificial intelligence models of the mid-2020s to the autonomous agentic ecosystems of 2026. This shift, colloquially identified as the "Action Pivot," represents a move away from the Large Language Models of 2024 and 2025, which served primarily as passive information retrieval and text generation tools, toward the deployment of agentic operating systems capable of executing system-level commands, managing multi-tool workflows, and interacting directly with corporate infrastructure. Central to this transformation is the OpenClaw framework, an open-source phenomenon that has redefined the boundaries of enterprise automation by enabling self-hosted, 24/7 autonomous agents on private infrastructure.
The emergence of OpenClaw marks the end of the "Chatbot Era," where user interaction was characterized by simple prompt-response cycles. In the preceding years, document review and AI assistance were limited to text extraction and basic contextual analysis. However, the introduction of OpenClaw catalyzed a surge in demand for systems that could take initiative. Within weeks of its release, the project amassed over 160,000 GitHub stars, eventually surpassing established software foundations like Linux and React to become the most-starred non-aggregator project on the platform. This viral adoption reflects a profound shift toward software that behaves as an active teammate rather than a passive tool, ushering in the Agentic Era of enterprise computing.
For the modern enterprise, the adoption of OpenClaw introduces a significant strategic paradox. The productivity gains offered by autonomous execution are substantial; organizations report up to a 70% reduction in operational costs and average resolve time improvements of 25-40% in customer support. Yet, the security profile of an agent with root-level privileges and the ability to execute shell commands creates an unprecedented threat landscape. The risk is structural: agents lack inherent sandboxing, and the modular "Skill" system—essentially an "npm for AI agents"—allows for the arbitrary execution of code that can exfiltrate sensitive data or move laterally through a network. Successful transformation requires a move beyond hobbyist local installs toward a hardened, cloud-native architecture grounded in three essential pillars of governance: Infrastructural Isolation, Behavioral Guardrails, and Human-in-the-Loop Accountability.
Hardening the Foundation: From Local Scripts to Cloud-Native Infrastructure
A primary obstacle to secure enterprise adoption is the prevalence of "Laptop-Ops." In many organizations, adoption begins as shadow IT, with developers or executives running the framework as a background daemon on their personal corporate laptops. This setup creates a lethal trifecta of risk. First, sensitive API keys are often stored in plain-text configuration files on the local machine. Second, the agent has unrestricted access to the local file system, including source code, customer data, and personal documents. Third, local machines lack the redundant power, network stability, and security monitoring required for 24/7 autonomous operations, leading to silent failures or unmonitored security breaches.
To mitigate these risks, the enterprise must mandate that all agentic deployments occur within containerized templates. This approach ensures that agents operate in a blast-radius-limited sandbox where their access to the underlying OS and network is strictly controlled. A hardened cloud-native deployment provides critical security advantages, including network isolation via strict firewall rules and OS optimization that reduces the attack surface by removing unnecessary desktop-oriented services. As organizations move from pilot to production, the operating system can be tuned to handle concurrent connections and high file descriptor limits, ensuring stability during complex task execution.
The shift to agentic AI also requires a fundamental rethinking of identity and secret management. Traditional models, where humans occasionally rotate credentials, are insufficient for agents that may require hundreds of unique OAuth tokens and API keys to perform a single multi-step task. To achieve production-grade reliability, enterprises must transition from local configuration files to enterprise-grade vaults. A dedicated token vault serves as a single source of truth, enabling dynamic issuance where a secret is created only at the moment the agent needs it, scoped specifically to the task at hand, and set to expire within minutes. This design ensures that raw API keys are never seen by the model itself; the agent receives only the result of the API call, preventing keys from leaking into chat history or downstream outputs.
Behavioral Governance: Managing Autonomy without Breaking Agility
The primary challenge in governing agentic AI is maintaining the agility that makes agents valuable while implementing enough control to prevent catastrophic errors. Unlike traditional software, agents exhibit non-deterministic behavior; they make decisions at runtime based on their interpretation of goals and external data. This requires a move toward dynamic behavioral governance, focusing on the audit of modular extensions and the implementation of machine-readable policies.
OpenClaw's modularity is driven by "Skills" distributed through community marketplaces. These skills are not merely plugins; they are executable scripts that carry prompts and instructions that become part of the agent's context. The ClawHavoc poisoning campaign recently highlighted the risks of this ecosystem, where malicious skills—disguised as office tools or crypto monitors—used social engineering to trick users into executing commands that installed malware or reverse shells. A zero-trust audit framework is necessary for any production-grade deployment, involving static code analysis, semantic review of prompts to detect hidden directives, and sandbox detonation to monitor network activity before a skill is approved for general use.
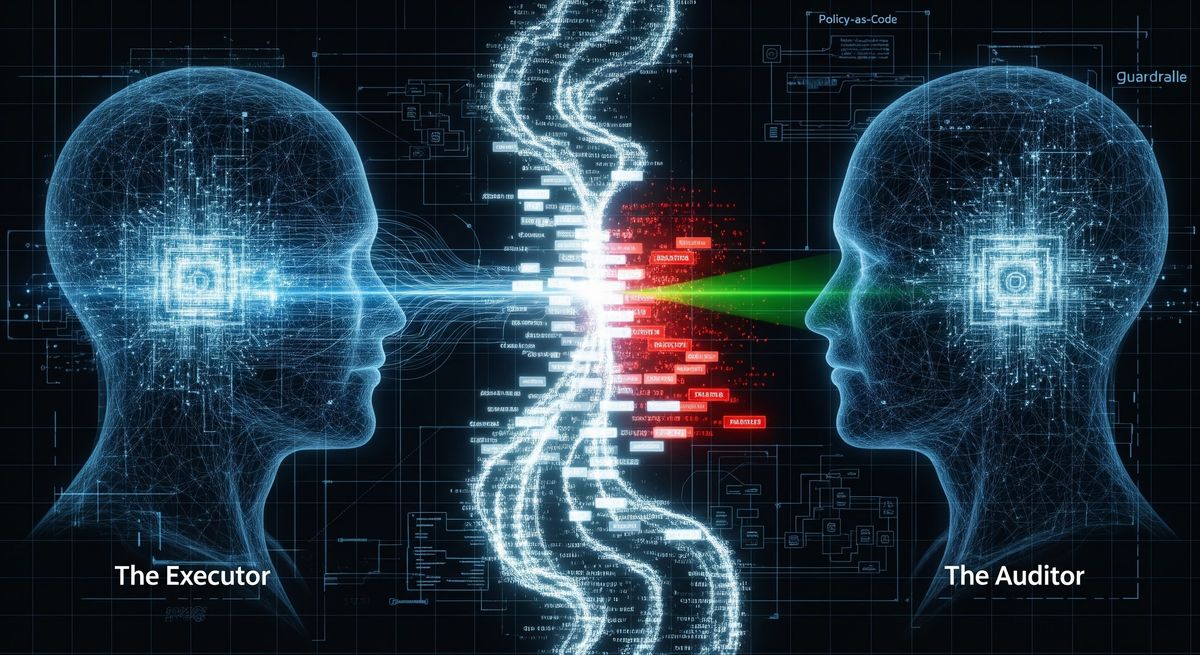
To govern AI at scale, enterprises must transition to Policy-as-Code. This approach expresses governance rules as machine-readable code that can be automatically enforced at the moment an agent attempts an action. In this model, the agent is free to move quickly and make decisions within a predefined "box" of safety guardrails. If the agent proposes an action that exceeds these limits—such as a request to delete a database or a financial transfer above a certain threshold—the policy engine blocks the request or escalates it for human approval. This provides the necessary enforcement layer between the agent and the infrastructure, translating high-level organizational intent into concrete constraints.
Furthermore, prompt injection remains the most critical vulnerability in the agentic era. Because agents process untrusted input—such as emails, web search results, or document attachments—they are susceptible to instructions hidden within that data. A promising defense is the use of dual-LLM architectures, where a dedicated security filter model analyzes all incoming queries and external data for potential threats before passing them to the primary executor model. This dual-layer approach has been shown to block a significant majority of identified attacks with manageable latency overhead, providing a defensive barrier that heuristic filters cannot match.
Operational Observability: Maintaining an Audit Trail at Agentic Speed

The non-deterministic nature of AI agents means that traditional software monitoring is no longer sufficient. IT teams must implement AI Observability to understand not just whether an agent is running, but why it made a specific decision. This requires moving beyond static dashboards toward an environment where teams maintain an audit trail with traceable run IDs, allowing them to reconstruct the agent's reasoning path by linking every prompt, model response, tool call, and system change into a single chronological narrative.
Effective structured logging should capture prompt input, reasoning steps, tool sequences, and final results. This visibility is critical for identifying runaway loops, where an agent gets stuck in a repetitive cycle of reasoning without reaching a conclusion. Furthermore, real-time cost and token quota tracking are essential. In the agentic economy, AI tokens are a metered utility where the cost of output tokens can be significantly higher than inputs. Agentic workflows, because they are iterative and involve self-correction, can burn through tokens much faster than standard chatbots. Without strict safeguards, runaway agents can trigger exponential billing spikes during complex, multi-step loops. Enterprises must implement token-aware rate limiting that can throttle or terminate processes if consumption velocities exceed predefined ceilings.
Finally, 24/7 AI-service usage monitors are required to detect behavioral drift. Security teams must monitor for unauthorized external connections or unusual patterns of command execution that might indicate an agent has been hijacked. By assigning a clear owner to every agent and focusing on building a data foundation for monitoring its lifecycle from creation to deactivation, organizations can prevent "orphaned" agents from becoming permanent backdoors into the network.
Conclusion: Leadership in the Age of Autonomous Execution

The transition to an agentic enterprise is a fundamental cultural and operational shift. The winner of the AI race will not be the firm with the most agents, but the firm that can govern them most effectively at scale. As a significant percentage of enterprise applications prepare to embed task-specific agents by the end of 2026, leadership must address the AI Leadership Paradox to ensure that widespread investment actually results in deep functional integration.
Organizations that implement these controls early report exceptional returns, with deployments in sectors like telecommunications and eCommerce seeing substantial reductions in support workloads and increases in conversion rates. This move necessitates the rise of AIOps teams, where engineers spend less time fighting fires and more time guiding the autonomous systems that do the heavy lifting. By treating agents as privileged digital workers rather than simple scripts, and by building the necessary cloud-native infrastructure today, enterprises can turn the potential of the agentic OS into a reliable reality.
As we stand at the threshold of the autonomous economy, the challenge for modern leadership is clear: the transition from experimental AI to production-grade agentic orchestration requires more than just code—it requires a foundational shift in how we manage trust, security, and accountability. By moving away from "Laptop-Ops" toward hardened, cloud-native infrastructures and implementing real-time behavioral governance, enterprises can finally unlock the immense productivity potential of the agentic OS while creating sustainable impact. The roadmap to success is built on the three pillars of infrastructural isolation, behavioral guardrails, and human-in-the-loop oversight. For organizations ready to lead this transformation and bridge the gap between innovation and reliability, partner with ATS to architect a secure, scalable future for your autonomous enterprise.